Contactless cards and mobile payments have made shopping quick and easy. A small tap at the checkout, and the payment is done, no PIN or swipe. But behind that convenience is a new and sneaky trick called “ghost tapping,” where scammers can charge your card without you even noticing.
This article will explain how the wireless tap-to-pay scam works and provide important tips for protecting your cards.
BBB Warns About Ghost Tapping Scams
The Better Business Bureau, a nonprofit that helps people find trustworthy businesses, is alerting the public after receiving numerous reports of ghost tapping scams .
In one case reported to the BBB Scam Tracker, a man has been going door to door claiming to sell chocolate to raise money for students with special needs. He tells people he can only take payments through a tap-to-pay card. Once they tap, he secretly charges much larger amounts than expected. One victim’s mother lost $537, and another person was charged $1100. To avoid being caught, he moves from one neighborhood to another [1].
To understand ghost tapping, it helps to know how Near Field Communication (NFC) works. This technology powers tap-to-pay systems like Apple Pay, Google Wallet, and contactless credit cards, letting devices communicate only when extremely close together, usually within about 4 centimeters. This short range is meant to make payments secure, but it is not foolproof. Portable NFC readers are cheap, handheld, and easy to hide, which means a fraudster in crowded areas can trigger a payment without the victim noticing.
How Scammers Steal Using Tap-to-Pay
Scammers use ghost tapping to steal money from people who trust tap-to-pay systems. They take advantage of how fast and convenient this technology is. Here are some common tricks they use:
- Getting close in public: In crowded places, scammers might bump into you and secretly use a hidden NFC reader to charge your tap-enabled card or phone.
- Fake vendors: They may set up fake stalls at markets, events, or festivals and ask for tap payments for non-existent goods or services.
- Charity scams: Some pretend to collect donations but charge a much higher amount than they say.
- Rushing the payment: Scammers often pressure people to tap quickly without checking the business name or transaction amount.
Protecting Yourself from Ghost Tapping
Protecting yourself from ghost tapping doesn’t require technical expertise, just a bit of awareness [1]:
- Double-Check Before You Tap: The best defense is prevention. Always ask to see the payment amount and merchant name on the terminal screen before holding your card or phone near it. If the person processing your payment refuses to show you the screen, be suspicious.
- Ask for a Receipt Every Time: A legitimate merchant will always be able to provide a receipt. If someone claims their machine is “broken” or “can’t print one,” that’s a strong sign to walk away. Receipts also serve as essential proof in case you need to file a dispute.
- Turn On Transaction Alerts: Most credit card apps let you turn on instant notifications for every transaction, giving you a first line of defense by alerting you immediately to any unauthorized charges. Scammers rely on people not checking their accounts often, so regularly monitoring your transactions can help catch fraud early.
- Block Contactless Payments When Not Needed: Temporarily turn off contactless payments through your bank app in risky situations, such as when traveling, in crowded areas, or if you don’t use them often.
- Report Fraud Quickly: If you notice unauthorized charges, contact your bank or card issuer immediately to dispute them. You can also report scams to your local authorities so they can take action.
Credit Card Scams Are on the Rise
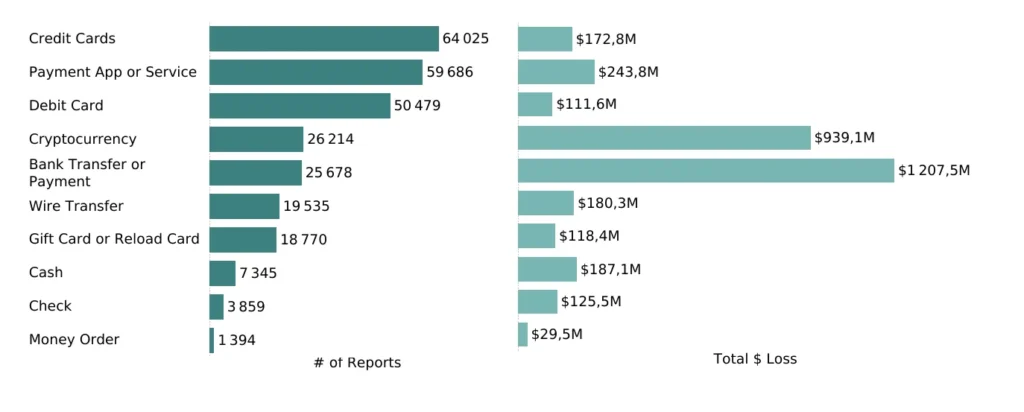
In the first half of 2025, the FTC received over 64,000 reports of credit card scams, with losses totaling $172.8 million, making credit cards the most commonly reported payment method for scams during that period (see Fig. 1). Scammers exploit people’s trust in credit cards to trick them out of their money.
Ghost tapping is just one form of credit card fraud. Scammers also use other methods to trick victims and steal money through credit cards (read more in our article):
- Skimming: Fraudsters attach hidden card readers or cameras to ATMs, gas pumps, or other payment terminals to secretly capture card information and PINs. These devices can be small and hard to notice, often fitting over the card slot or keypad. Once your card is swiped or inserted, scammers can clone it and use the information to make unauthorized purchases.
- Phishing: Scammers send fake emails, texts, or social media DMs that look like they’re from your credit card company or bank. They might claim there’s a problem with your account or a suspicious charge, asking you to click a link or share your card details. Once you do, they can steal your credit card information and use it to steal your money.
- Malware: Scammers can install malicious software on your phone, tablet, or computer to steal credit card numbers, login details, or other sensitive information. This lets them access your account and make unauthorized charges or withdrawals without your knowledge [3].
Eydle’s Online Protection
Scammers are constantly looking for ways to turn convenience and trust into profit, and social media has become their newest playground, where they pose as trusted brands and send fake DMs to trick unsuspecting users. That is where Eydle comes in.
Our AI-powered tool continuously monitors your business’s social media profiles, messages, and comments to detect phishing attempts and identity theft before they can harm your customers or your business.
Learn how Eydle can help protect your business at www.eydle.com or reach out to us at [email protected].