Phishing is not just email — it’s social
To protect your brand online, protect its social media accounts
Phishing attacks are relentless. Is there anyone who hasn’t seen a phishing email? While it may seem that email is phishing’s BFF, times are changing. In the last two years, phishing on social media has become the number one online fraud attack. So what does phishing on social media look like, and what can you do about it?

What does it look like?
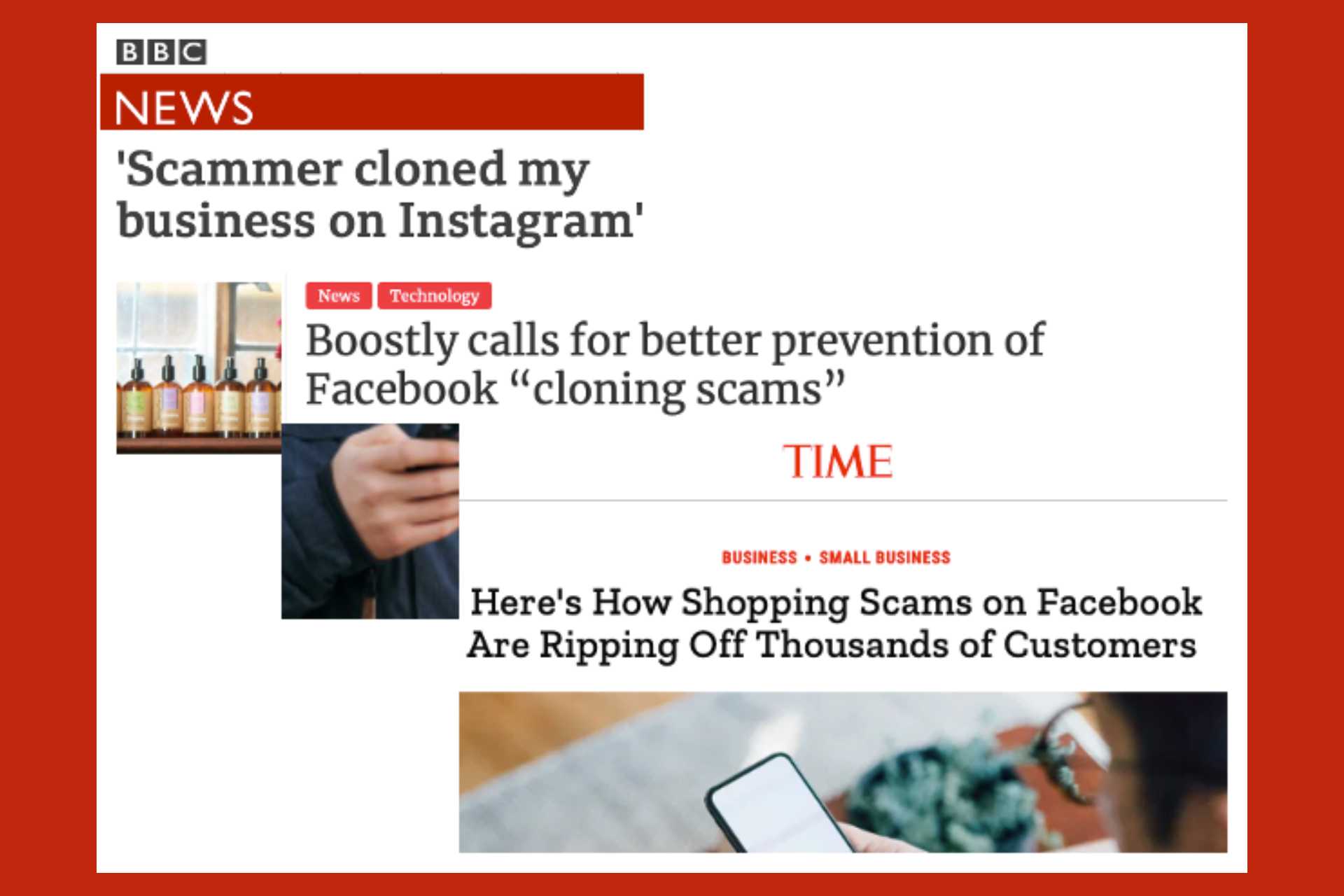
Cloning of Instagram and Facebook business accounts is a classic example of phishing on social media. It is more common than you may realize. There are 200 million businesses on Facebook and Instagram alone that are at risk every day. Consider the hospitality industry for instance. Perhaps a bed and breakfast offers an annual giveaway of 2-night stay through its Instagram account. A scammer will clone the B&B’s Instagram account by creating another Instagram account that looks very similar to the original by copying over images and logos from the original account. The scammer will then message the B&B’s Instagram followers that they have won the giveaway and should submit their credit card information in order to receive the 2-night stay. Because the cloned account looks similar to the B&B’s account, usually some followers fall victim and submit their information to the scammer.

Another example of phishing on social media is a bogus ad. On the left, you see an example of a bogus ad (dated May 17, 2021) on Facebook impersonating Netflix. If you pay close attention, you will observe that the “Give Away” is not actually sponsored by Netflix. If you were to click on the ad, it would collect personal information in the pretext of giving you the $60 gift card.
What is the impact?
Both cloning and bogus ads impersonate legitimate brands and trick the brand’s social media followers and customers. Social media phishing and brand impersonation is a reputation risk for big and small brands alike. Brand reputation built overs many years can be damaged in a single attack. Controlling the damage from an attack — placating scammed customers, dealing with negative reviews and trying to take down the clone accounts — requires a brand to allocate resources away from its core business. Connecting back to the B&B example above, the business owner has to handle a deluge of calls from angry customers demanding an explanation. They have to deal with negative reviews written by customers who mistakenly believe that the B&B scammed them. Businesses have reported allocating 2–3 staff members working 3–7 days full time to deal with the fallout. Allocating that much resource is a burden for small businesses. Although larger enterprises have more resources, they also have to deal with a much larger volume of attacks. Hence, burdensome even for large enterprises.
What can businesses do?
If a business finds a clone account, it can try to take down that account by reporting it to the social media platform. Many social media platforms have a process for taking down impersonation accounts. On Instagram for instance, a business account user can report that “Someone created an account for my business or organization.” However, the onus is on the user to provide adequate evidence for proving their claim. Before filing the report, the user needs to understand whether the clone account violates Instagram’s terms of service/community guidelines or it infringes the business’s intellectual property. This is important because Instagram will use it as the basis for taking down the clone account. If the user does not select the appropriate option, Instagram may decline to take down the clone account.

In addition to reporting a clone account, businesses can monitor for clone accounts. Some common techniques include reverse image search, hashtag search and keyword search. Businesses can also monitor @mentions and scan posted comments for malicious links. Although monitoring on a weekly or bi-weekly basis can be time-consuming, it can provide some protection against cloning and impersonation attacks.
Businesses can also look for end-to-end solutions that can monitor, detect and take down impersonation accounts. Here, it is important to pay attention to pricing, technology requirements and whether the solution caters to the needs of large enterprises or small businesses. At Eydle, the startup I work for, we are building a solution with the needs of both small and large brands in mind. Contact me to learn how Eydle’s solution can help.
In future posts, I will discuss the take down process on different social media platforms and provide more information on techniques that businesses can use to monitor for clone accounts. If you are a business impacted by social media phishing, share your experience by leaving a comment below.
Phishing is not just email — it’s social was originally published in Eydle on Medium, where people are continuing the conversation by highlighting and responding to this story.